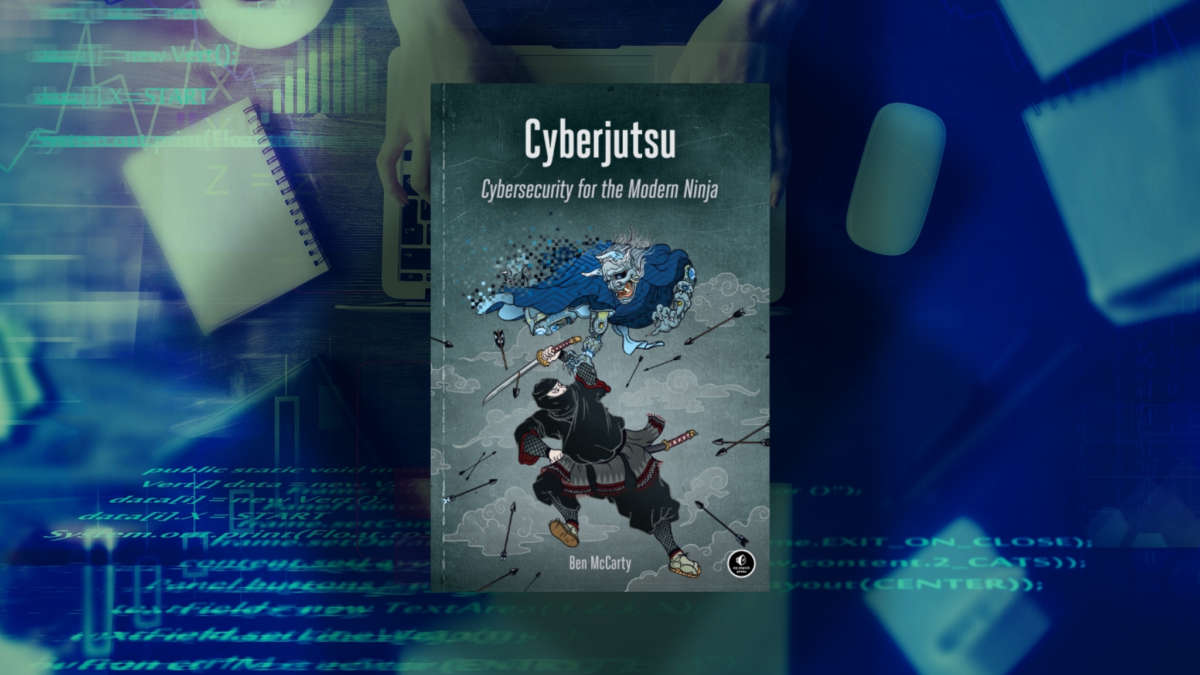
Cyberjutsu,
Our digital lives depend on cybersecurity. When hackers broke into the computer networks of Home Depot, Staples, Target and Equifax in recent years, customers became victims of identity theft, their credit card numbers stolen and their credit histories compromised.
Today, even our national security is threatened. The SolarWinds software breach in December gave hackers, likely of Russian origin, access to the sensitive information of nine federal agencies including the Treasury, Homeland Security, State and Energy.
“Cybersecurity has never been this critical to our economic prosperity and social peace,” is the first sentence of Cyberjutsu, a new book by Ben McCarty from No Starch Press, publishers of “the finest in geek entertainment” such as computer programming, operating systems and security.
Writing for a rapidly growing workforce of specialists tasked with protecting network security, McCarty draws inspiration from the training methods of feudal Japan’s legendary ninjas. “The deepest principle of ninjutsu (ninja arts, skills and techniques) is to avoid where the enemy is attentive and strike where he is negligent” — cyber tools practiced by armies and covert operatives to this day, writes McCarty.
CYBERSECURITY CONCEPTS AND NINJA LORE
A former National Security Agency developer and the U.S. Army’s first Cyber Warfare Specialist, McCarty noted by e-mail that he wrote Cyberjutsu for both cybersecurity experts and those outside of the field. “I really wanted to share the novel attack/defense techniques of the ninja with cybersecurity professionals. I also wanted to make it approachable so most people could grasp the concepts and ideas behind these secret ninja techniques, while also providing an insight into the security industry.”
McCarty added that he was inspired by The Secret Traditions of the Shinobi: Hattori Hanzo’s Shinobi Hiden and Other Ninja Scrolls (Blue Snake Books, 2012), a translation of historical manuals passed down in ninja families for hundreds of years. He recognized that he could link cybersecurity concepts and ninja lore. “My mind kept coming back to the scrolls after I read them and the ideas behind them kept gnawing at the back of my mind for years. Eventually, I had enough and decided the only way to stop this persistent mental distraction was to put all those thoughts in a book and be done with it,” commented McCarty.
PRACTICAL AND PRESCIENT
This book is not an “idiot’s guide to cybersecurity.” It’s heavy with tech acronyms and security concepts, and though it deciphers the acronyms, some prior understanding of security-strengthening methods is required for the book to be of practical use. Still, its ninja-fueled tactics, techniques and procedures (TTP in cyberlingo) may appeal to organizational leaders in the same way they might turn to Sun Tzu’s The Art of War to level up their plan of attack.
The book is also a good overview of cybersecurity for students and anyone considering a career in this expanding field. In fact, it’s expected to increase by 31 percent in the next decade, according to the Bureau of Labor Statistics, making books like this one highly useful. McCarty attributes this rapid job growth to organizations now realizing the merits of creating dedicated roles for security responsibilities.
“Many organizations may have previously had an internet technology/network engineer tasked with two responsibilities — to both run and secure the tech,” he writes. “Now that role is being split into two jobs. While many IT people are perfectly capable to do many types of security work, it can create a conflict of interest when their primary duty is to maintain IT operations instead of prioritizing security.” There’s clearly so much on this horizon. Cyberjutsu, with its knowledge of the past and its applications for the future, is sure to inspire both cybersecurity insiders and the curious.
For more information on McCarty, visit his BookTrib author profile page and check out our interview with the author here.