Cyber is the new normal, isn’t it? Especially in our current climate where everything is done online. Just think about how many activities, from work to working out, have transitioned from needing a commute to needing nothing more than a new tab opened. Our computers have practically become another appendage. Now when you realize just how closely your computer holds all your crucial everyday information, and how close all that information is to a stranger’s grasp, you realize you may need to brush up on your cybersecurity.
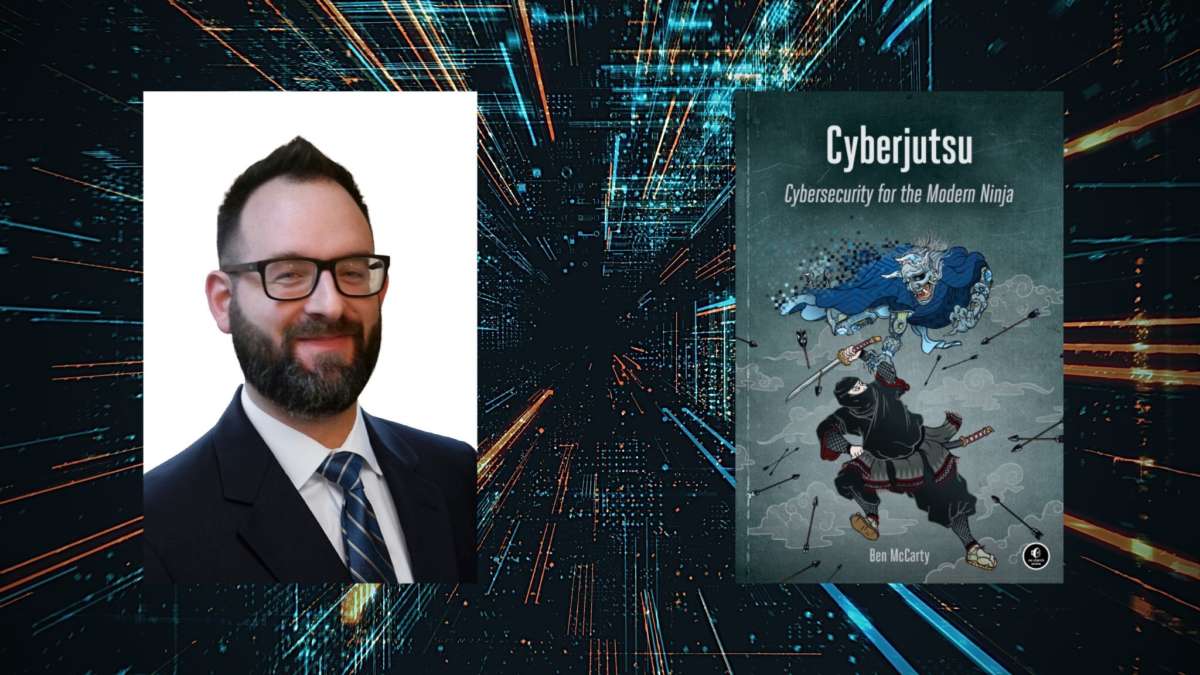
Do you know what other skills you could use for self-defense? Ninja skills. I bet you never thought, though, to put ninja arts and cybersecurity together to maximize your chance of success against those insidious invisible enemies we call hackers. Thanks to Cyberjutsu, you can now harness the power of this surprising combination and have a better-protected online presence.
BookTrib was able to ask author Ben McCarty some questions about his intriguing approach and his process in writing his book about it. To read a review of Cyberjutsu, you can check out our article here.
Q: How did you end up in the field of cybersecurity?
A: I received a $1 raise in my annual performance for a job; I was so outraged by it that I immediately stood up from my desk and walked into a U.S. Army recruiting office. I told the Army to give me the hardest technical job they had, and suddenly I was doing Cyber Warfare in the army as my first cybersecurity job.
Q: What made you realize that you could use the tactics of ninjutsu to improve cybersecurity?
A: After reading Antony Cummin’s translation of the Ninpiden in 2013 my mind was swimming with cybersecurity ideas. I couldn’t shake the ideas gnawing at me to do something with them.
Q: Could you give us (in layman’s terms!) an example of this?
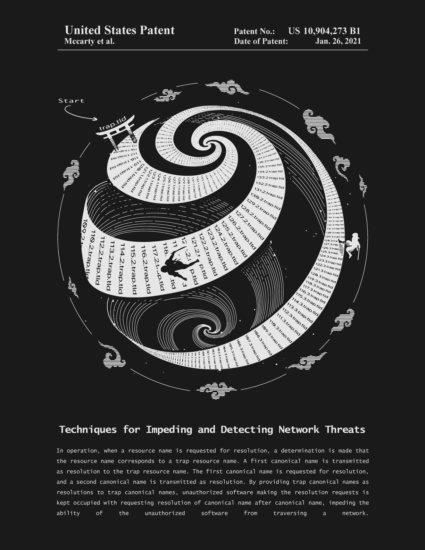
A: One of the tactics from the scrolls that I thought was particularly clever were Ninja traps or ambushes, which were adapted from tiger fall traps. I thought this idea of a trap could work for Ransomware and patented US10904273B1, a Ransomware trap that doesn’t require any signatures. I illustrated the Ninja concept and how it technically works in the following figure:
Basically, have you ever noticed that when you visit a site like www.booktrib.com it automatically changes to booktrib.com? Your computer asks a DNS server the IP address of www.booktrib.com but it instead directs you to booktrib.com, then your computer asks for the IP address of booktrib.com and is able to finally visit the site. But what if it was an endless stream of new redirections? Your computer would be stuck in an endless loop trying to get an IP address, but would just get more and more DNS names which it can’t actually visit.
Ransomware trying to maliciously spread everywhere through your network would hit one of these trap domains and get stuck, while also alerting you to its presence at the same time.
Q: What was your process in writing this book? How did you develop and organize your ideas?
A: I read as many ninja scrolls and texts as I could get my hand on. Then I reread the best ones over and over until I felt like I had internalized their knowledge. I used a paper notebook to organize all the ideas and collect all the references and notes on each topic. Then it was my own creative process in imagining how to apply these ninja arts to modern cybersecurity, and how to teach the principles behind the ideas so a reader might develop a deeper understanding of these security challenges.
Q: What do you hope readers will take away from the book?
A: I hope they will take some of these ancient, secret ninja skills and help solve or mature the cybersecurity industry so it moves a little bit closer to being safe and secure for everyone.
Q: Any new writing projects on the horizon for you?
A: I have two writing projects I am juggling right now. I’m working on the second book in the Cyberjutsu series, which will teach quantum security concepts for both quantum computers and the quantum internet; the other project is a high-fantasy fiction novel with dragons, wizards, knights and artificial intelligence (AI). I will try to write it so it can be adapted, hopefully, into a video game in the distant future.
Learn more about McCarty on his BookTrib author profile page.
https://booktrib.com/wp-content/uploads/2021/04/BookTrib-Ben-McCarty-Thumbnail.jpg
About Ben McCarty:
Ben McCarty is a former Cyber Capability Developer with the National Security Agency (NSA) and served as a Cyberwarfare Specialist in the U.S. Army. He has multiple security certifications, patents and years of experience working in the security industry.
He served in the U.S. Army’s Network Warfare Battalion and became the first fully qualified cyberwarfare specialist (35Q) in U.S. Army history. McCarty has multiple pending security patents in DNS, Blockchain, Biometrics, and Quantum.
He wrote his first book, Cyberjustu: Cybersecurity for the Modern Ninja, which was published by No Starch Press, in 2021.